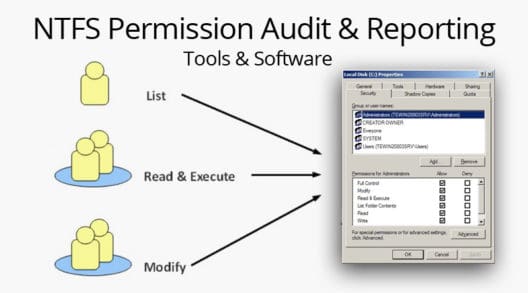
Here’s the Best Tools for Windows NTFS Permission Auditing and Reporting – [ Analyze Active Directory, Shares, Files/Folder and More with These DOWNLOADS! ]
The Best Windows NTFS Permission Auditing & Reporting Tools
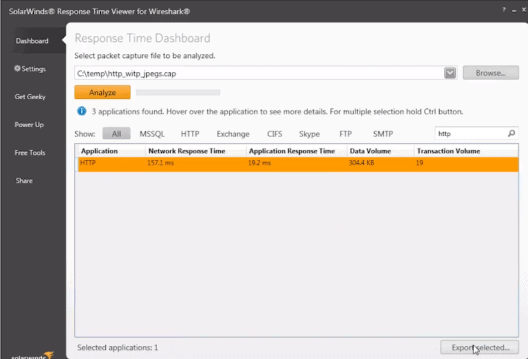
Analysis of Wireshark Response Times using a Free TOOL – Tutorial!
Solarwinds’ Response Time Viewer for Wireshark is a standalone tool that analyzes the packets captured by Wireshark, so you can get in-depth information about your network in a dedicated viewer. This tool is a great one for troubleshooting network problems as you can analyze most common packet formats. Typically, you should use Wireshark for capturing […]
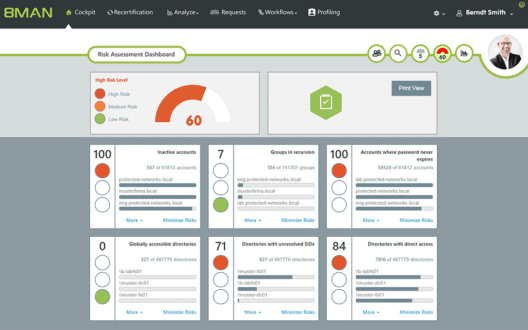
Access Rights Manager Review – How to Audit AD Permissions, File Shares & More!
/ August 25, 2023 — SecurityAuditing Active Directory, File Permissions, File Shares and More is Now Easier than Ever from a Centralized Location using Solarwinds Access Rights Manager, Here’s why!
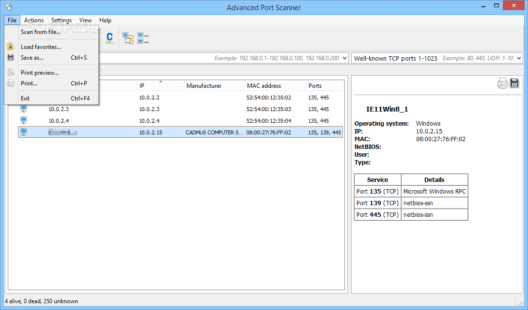
Port Scanners for Scanning Windows/Linux Systems for Open Ports/Service
Port Scanners are an important tool when you want to investigate any remote or local network for security considerations. Used by programmers and network administrators, these port scanners are used to mainly know what ports are being used by what applications, so you can identify malicious programs right away. These port scanners can also be […]
Advanced Port Scanner – A Review of one of the Top Port Scanning Tools on the Market
/ December 14, 2022 — SecurityAdvanced Port Scanner is a Versatile Port Scanner that is 100% FREE – You can scan local networks and remote Networks (LAN & WAN) Fast & Free from Any computer!
Visualizing Network & Bandwidth Activity with GlassWire
GlassWire is a new type of graphical network monitor for Windows that focuses on endpoint monitoring. The software runs on Windows 7, 8, and 10, and there is also a version of the app for Android. Setting up GlassWire for Windows is fairly simple and only requires using a Windows installer that can be downloaded […]
The Best Network Security Software & Frameworks for Pen-testing & Vulnerability Assessment
Finding Vulnerabilities and Exploits/Holes in your network infrastructure should be something you Do before a Hacker finds them – We’ve highlighted the Top Tools for Network Security Assessment, Vulnerability Scanning and much more!
WordPress Security and Available Plug-ins
WordPress is one of the most popular website platforms for bloggers and businesses as of 2017. It is easy to use and flexible as well as highly supported by developers and designers, but its security should also be considered. WordPress Security Issues It is a sad fact that a great many websites have been hacked […]
IPC$ Security Trick
It is possible to establish a security context with another domain by using the net use command. Syntax: net use \\<server name>\IPC$ /USER:<domain>\<account> Explanation: If you want to manage the Booky domain, with a PDC called Kooky, and you had an administrative account on Booky called bookadmin, you could use: net use \\kooky\IPC$ /USER:BOOKY\bookadmin you […]
TCPDump Lab
We picked up a DEC Alpha Multia cheap at auction a couple years ago. We will use this multia to dump the network traffic that NT creates on boot using TCPDump. The first problem we had was that our Multia is not Y2K compatible. Many of our files ended up with dates of 2019, and […]
NIMDA Scanner
Free NIMDA Scanner checks for known NIMDA worm files (admin.dll, load.exe, readme.exe, etc.), checks your system.ini, and remotely checks “Administrators” group for “Guest” account. Click here to download. [Beware of running free programs that scan for viruses… better look that gift horse in the mouth. 🙂 Ed.]
Nmap Port Scanner
Nmap is a free port scanner you can use to audit your own network and ensure the security of your hosts from outside your firewall as well. It is also entirely likely that your external interfaces are being scanned at this very moment with Nmap, or tools like it. One cool thing about Nmap, is […]
Baseline Security Analyzer
Do check out the Baseline Security Analyzer tool from Microsoft. Just download the MSI package from the page and install it with a shortcut on the Desktop (default). We ran it against a fresh Windows 2000 install with just SP2 installed. Here is a screenshot of the results. We are alerted to many security issues. […]
Quick and Dirty Host Block
If you are being attacked or abused by a particular host, just enter the following command to deny all access to the host: /sbin/route add -host <ip address> reject Replace with the IP address of the host you want to block. The address will stay blocked until you bounce the interface. Alternatively, you could allow […]
Virus Test File
Check out the European Institute for Computer Anti-Virus Research (eicar) Anti-Virus Test File page. EICAR provides test files you can send to your users to determine if their anti-virus software is functioning correctly. We’ve seen this work fine on Trend Micro and Norton Anti-Virus software, but most ant-virus software should correctly detect these files. To […]
A Trojan in Every Port
If you have any kind of intrusion detection set up like Psionic’s PortSentry or a personal firewall, you’ll see attempts to connect on ports you may not be familiar with. Even looking up the port in /etc/services doesn’t tell the whole story. To find all known network services, trojans, worms and exploits associated with a […]
Keylogging
Like anything else, keylogging can be used for good, or for evil. Here is a list of related links, including both hardware and software keyloggers. (Yow!) Regardless of the privacy issues, there are also security issues as well. Some trojans will install keylogger software as part of their kit. There are also keyloggers geared for […]
Block IP Addresses With IPtables
We wrote about blocking particular IP addresses with the route command here. If you are already using iptables, or want to start, a better way is to block particular hosts: iptables -I INPUT -s 25.55.55.55 -j DROP This command will simply drop any packet coming from the address 25.55.55.55. To list the chains: iptables -L […]
Encrypting Files Conventionally With GnuPG
Conventional encryption is where there are no keys involved. This can be done with the -c option on GnuPG. When you use this option you will be asked for a passphrase. To decrypt the file the same passphrase is needed. This is ideal for password lists, where you have the ability to share the passphrase […]
Windows Run At Logon Keys
One key to check on Windows boxen is the Run key. The run key is located in HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run. When a user logs on, the programs specified in the run key also run. Many times a trojan will install itself here. A lesser evil is the hordes of small little apps that like to run some […]